Conversation Hijacking
Blog post by Robert Marsh. Robert Marsh is a published Internet of Things Forensics Researcher and an award-winning Artificial Intelligence Software Developer. He is currently working as a Cyber Security Analyst with the Greater Manchester Cyber Foundry technical team at The University of Salford.
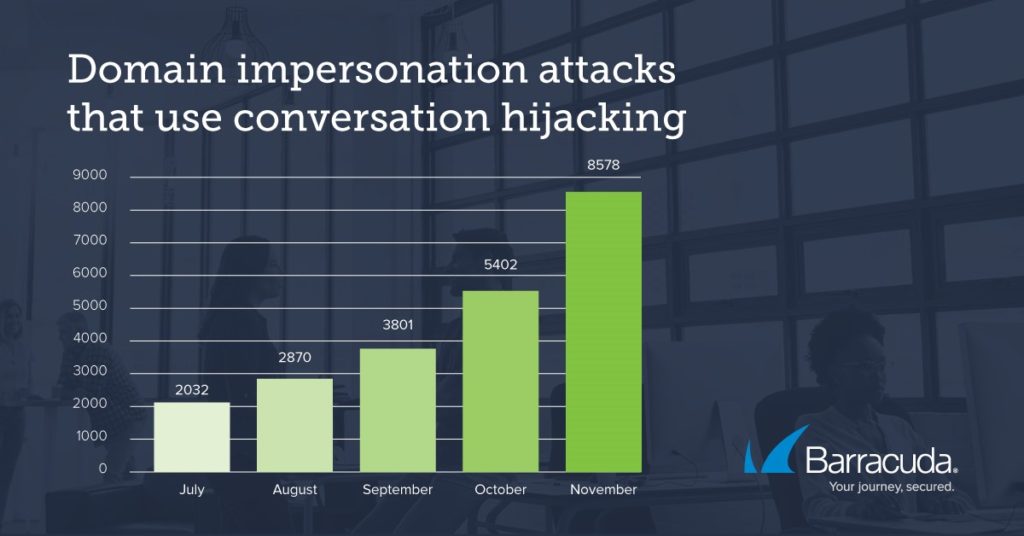
Conversation hijacking attacks are sophisticated, personal, effective, hard to detect and the repercussions are costly. Furthermore, recent analysis conducted by researchers at Barracuda showed a 400% increase in Domain Impersonation attacks used to facilitate Conversation Hijacking[1].
Cyber security professionals understand the difficulties in detecting compromised accounts. Automated detection tools and/or manual interventions are often required to flag and/or disable compromised accounts. Before the accounts can be handed back to their owners, they must be secure, or in the case of dormant accounts, deleted.

These hacked accounts may only be accessed by a cybercriminal for a matter of minutes before they move on. Often the attackers will record previous email transactions, contact lists, business information and anything else accessible to them. They do this using sophisticated tools that act quickly before they are locked out of the account.
Attackers leverage the harvested information to identify management structures inside organisations and to tailor phishing attacks. By impersonating authority figures within an organisation, attackers exploit the inherent trust of other employees. This type of sophisticated social engineering attack may require changes in the culture of an organisation or employee training (as the new norm would allow subordinates to question requests from their managers without fearing repercussions).
There may be no correlation between the breached account and the employee who is targeted by the conversation hijacking techniques. This makes it difficult to detect malicious activity, as a breached account would usually be monitored for suspicious activity after access is given back to the original user. The attackers merely use the breached account to harvest valuable information on the business, the employees, and their day-to-day activities.
Leveraging this information in an attack could be as simple as sending an email to the employee in charge of making payments, requesting that a fabricated bill is paid immediately. However, more sophisticated attacks have surfaced where the attacker will converse with an employee and pretend to be a more senior member of staff. This sometimes results in the conversation being continued on a less formal platform where they can bypass any corporate security protections that could prevent or mitigate the effects of the employee clicking on malicious links.
How to protect your staff
- Ensure that all business communication is conducted via authenticated business accounts that your organisation has control over. Avoid using personal accounts for work purposes e.g. WhatsApp, Facebook Messenger, FaceTime, etc to conduct business conversations.
- Encourage an open culture in which employees are comforable to double check all payments via an alternative authorised communication channel prior to the settlement. For example, if an email is received for a bill to be paid, check that the sender is genuine via a quick message on your company approved messaging platform e.g. Slack or Teams. Further to this, senior employees could send a message or call the individual first to say that they are about to send an email that requires a payment to be authorised.
- Other methods of protection exist such as detecting spoofed emails and blocking phishing/scam emails, however, they are the last line of defence. The first line of defence should always be having trained and aware staff who are following the businesses simple security procedures and protocols.
[1] https://blog.barracuda.com/2020/01/16/threat-spotlight-conversation-hijacking/