Money and trust in social VR: Cyber secure metaverses for business reach
Authors:
John O’Hare, Technical Director of Octave Lab and Bitcoin Researcher, University of Salford.
Allen Fairchild, GM Cyber Foundry Analyst Developer Team Leader, University of Salford.
Umran Ali, Senior Lecturer in Creative Media, University of Salford.
Lorena Gomez, GM Cyber Foundry Project Manager, University of Salford.
In the last couple of years, the Greater Manchester Cyber Foundry has been collaborating with small to medium sized enterprises, responding to their questions about emerging trends. We were asked about exciting new developments in the transmission of value, and trust in Metaverses. The problem is that each of these topics alone are enormously complex, and the intersections seem to be more so. We have been researching the current state-of-the-art, and the emerging consensus narrative, to try to figure out how the collision of these technologies might serve SMEs.
Because we’re the GM Cyber Foundry, we started out with security best practices in mind. How can we enable small and especially developing companies, to have a foot in the door on a global stage, without their cybersecurity costs spiralling? Fortunately, we discovered a wealth of carefully crafted open source tools which can support this exploration. We have tried to assemble them cogently, to deliver a kit for experimentation to curious technically minded SMEs, and we have applied our own security knowledge on top of an already top class set of tools. It’s certainly not production ready, but it’s good enough to commit small amounts of money into, for experimentation purposes.
Whilst researching, it seemed that every door we opened was full of interesting and useful treats. What was supposed to be a short technical paper quickly became a 150-page book, and a deployable virtual machine stack, with a dozen different open source components in it.
To that end, this post supports the book, which supports the virtual lab, which supports anyone who thinks this material might be useful. In the following pages you’ll read a precis of the chapters and sections of the book, which will hopefully give an insight into what “this stuff” is. Then you can decide to download the book and the lab how to guide. All of it is open source, all of it can be contributed to on GitHub, all of it will be developed forward, and none of it is really finished yet.
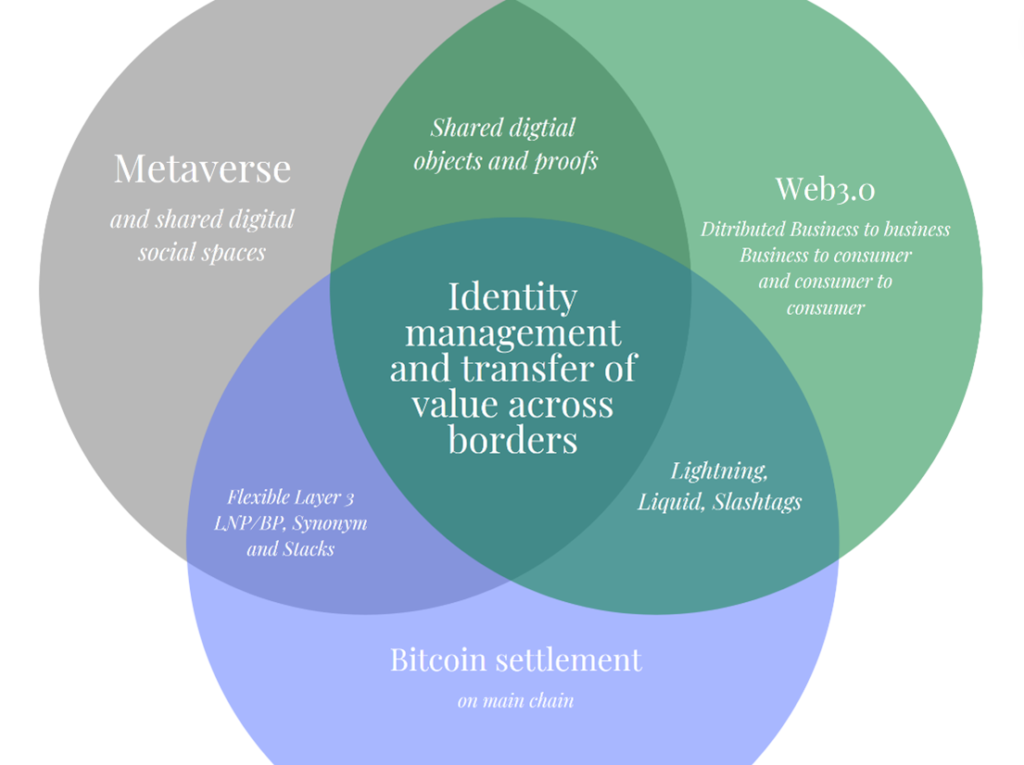
Chapter 1 attempts to overview what the book is about, which is value transmission, with distributed trust, in global social mixed reality systems. That’s this diagram:
Next is a summary of Web3, as it stands right now. Web3 is a complex term and it’s cropping up far more in the technical press so we wanted to cover off what it might mean, but honestly, it’s still pretty confusing. There’re a bunch of legacy explanations which are Web3, that are withering on the vine. Then there’s the new VC funded, super hyped and potentially useless Web3 incarnations, which again cover a slew of intersecting technologies. This doesn’t mean there’s nothing to see here. The astonishing amount of money and developer talent, and the clear market hunger for things like NFTs (non-fungible tokens) suggest that there’s a future for Web3, it’s just really unclear what the value could be for our curious SME.
In the next chapter we took a look at blockchain, which is very intersectional with Web3. Even on its own this is a very complex emergent set of disciplines. The diagram below is used with permission of Dhruv Bansal and shows just how vast this area is.
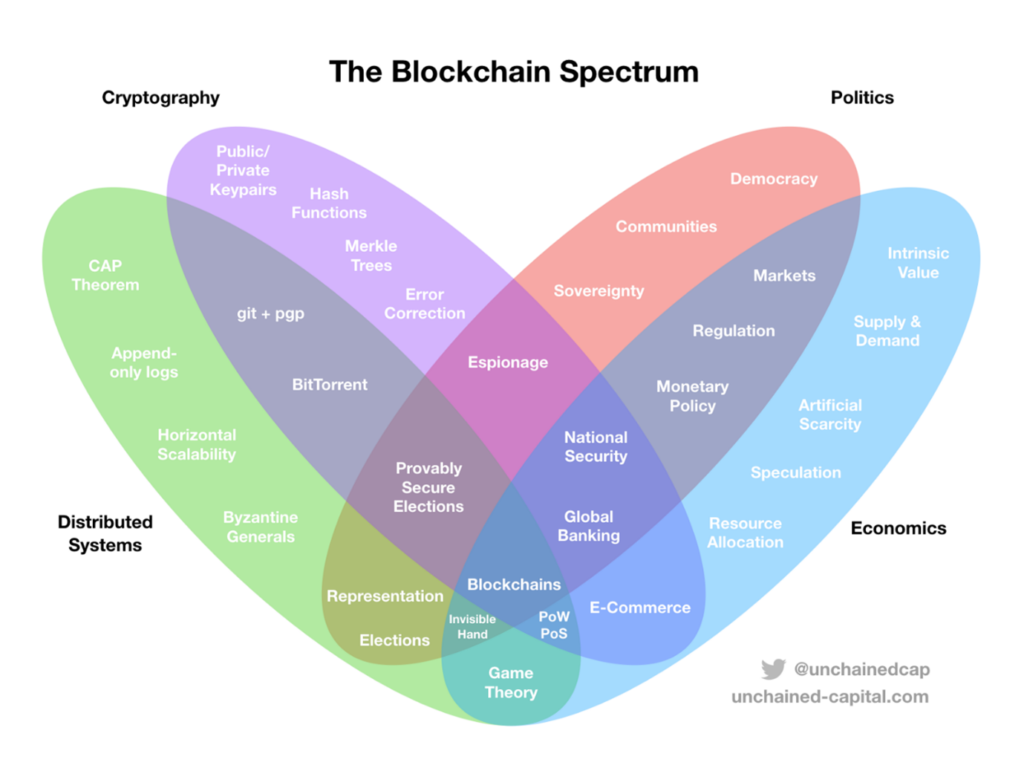
This blockchain chapter was especially interesting to research. It turns out there’s a LOT of ways to get this technology wrong. Even very appealing options on paper, turn out to have very shaky foundations. There are really valuable things here, but given the complexity, and the size of that chapter, we decided to focus down on the most promising of the technology stacks, which interestingly turned out to be the original; the Bitcoin network.
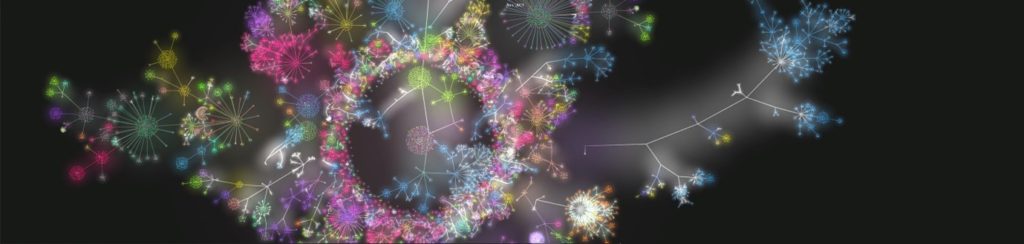
Even Bitcoin isn’t just Bitcoin anymore. It’s a swarm of open source tools which can (in theory) accomplish a great many things (see Figure 4 which is a visualisation of code commitments to the various open source software repositories used with the permission of the artist Bitpaint). These newer, ancillary elements to Bitcoin, are emergent right now. Some of the won’t be around until later in the year and it’s questionable whether they will even work out. With that said there’s already enough here for us to cherry pick some useful components and start to map those forward into our metaverse proposal.
In looking around at the available options, it seems possible that the features which are important to Web3 in chapter 1, can also potentially arise from the Bitcoin technology that we settled on in section 2. This was somewhat unexpected, so we started mapping that over too.
The next chapter is about Money. In expanding our research on Bitcoin, we found that it’s impossible to think about the tech without opening up a whole other line of questions about money itself. This is fine because we set out to look at global value transfer for business. It’s not a trivial subject though, and this chapter tries to overview why value and Bitcoin are so enmeshed then what other options there might be in the end (because Bitcoin has kicked off a whole slew of global adoption outside of itself) and finally what we can do pragmatically, both now, and in the coming year or two.
The distributed identity management, and trust chapter follows. It’s not an easy chapter to write about, because there’s a lot of research, it’s not our field, and finding the value to SMEs has actually been very difficult. This chapter is likely to be overhauled a few times in the coming months as we settle on technologies that we believe are simple and secure enough.
In chapter 6 we take another look at NFTs. It’s impossible to ignore this stuff now. It’s fundamentally a bit broken, but there are likely some use cases, and the money and development attention it’s getting are incredible. We try to navigate our hypothetical SME through this as best we can. It’s not that we didn’t understand it completely, just that the tech moves so very fast that it’s impossible to even describe what’s going on accurately at any given point. We’re actually pretty excited about future versions of this technology, based around Bitcoin, because that allows us to keep just one value stack in the lab. We’ve mapped that forward into the open source tools that we recommend. This very much ended up looking like our priors; our cyber security values, and our wish to build toward a simpler product using only Bitcoin. To that end we asked another author, with much more of a foot in the content creation world, to collaborate with us on this chapter. This will benefit from smoother integration over the coming months.
Chapter 7 is a big one for us as it’s our research area prior to opening up the Bitcoin box(es). Metaverse, or at least one of the current definitions of metaverse, is just social interaction in mixed reality (VR/AR/XR!). We’ve been studying that for decades, so this chapter is more academic and tried to boil down what we think is most important to map forward into the lab. The choices we make here guided us toward the selection of free and open source metaverse software, which we selected from a bunch that we reviewed. You can make your own choices and gain insight from the systems we looked at.
We also take a look at the other definitions of metaverses which are doing the rounds on the web, try to unpick which is which, and what they are for, then we attempt to weave back together the best of both. This ends up looking a bit like the Venn at the top, where we have transmission of provable identity, non-fungible tokens bearing value or data, distributed files, actual money (including micropayments) and a social layer based on our best knowledge about mixed reality.
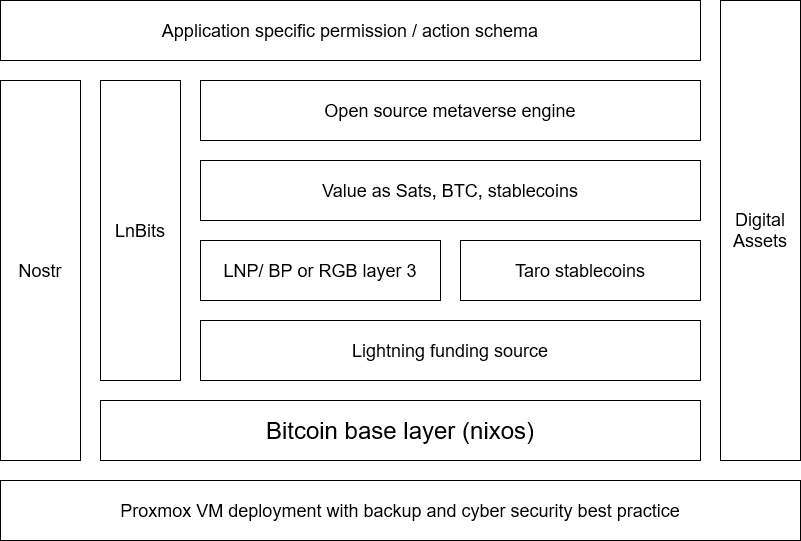
The virtual machine and tech stack are detailed in section 2 of the book and in the Lab section of the GitHub repository. This is a detailed technical walkthrough to setup the components to date. A Proxmox Virtual Environment is configured, including choices about memory and storage. A cybersecurity gateway is configured and integrated with the local networking so it can act as a gateway to the outside world. On top of these elements we deploy a basic economic stack using a hardened version of Bitcoin and Lightning, and an open source metaverse server.
Here are the latest versions of the book as a PDF, and the GitHub repository.